DKIM and DMARC with SAP Commerce
What are DMARC and DKIM?
DMARC (Domain-based Message Authentication, Reporting, and Conformance) and DKIM (DomainKeys Identified Mail) are email authentication protocols used to combat email fraud and protect against email spoofing and phishing attacks.
DKIM:
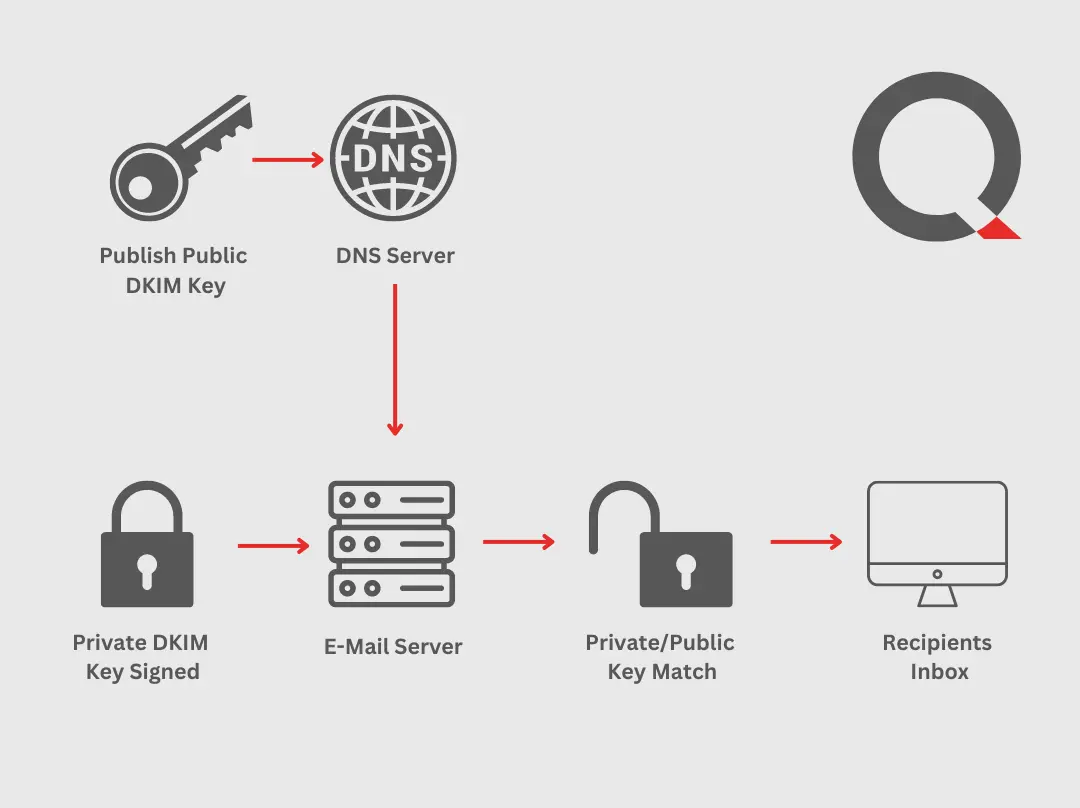
DKIM is a method for email authentication that allows the sender to associate a domain name with an email message. It uses digital signatures to verify the authenticity of the email and ensure that it has not been modified during transit. When an email is sent, the sender's email server adds a digital signature to the message header using a private key associated with the sending domain. The recipient's email server can then use the public key published in the sending domain's DNS (Domain Name System) records to verify the signature and determine if the email is legitimate.
By implementing DKIM, email recipients can check if the email's domain matches the domain it claims to originate from. If the signatures match and the email passes the verification process, it provides a level of assurance that the email is genuinely from the claimed sender and hasn't been tampered with.
DMARC:
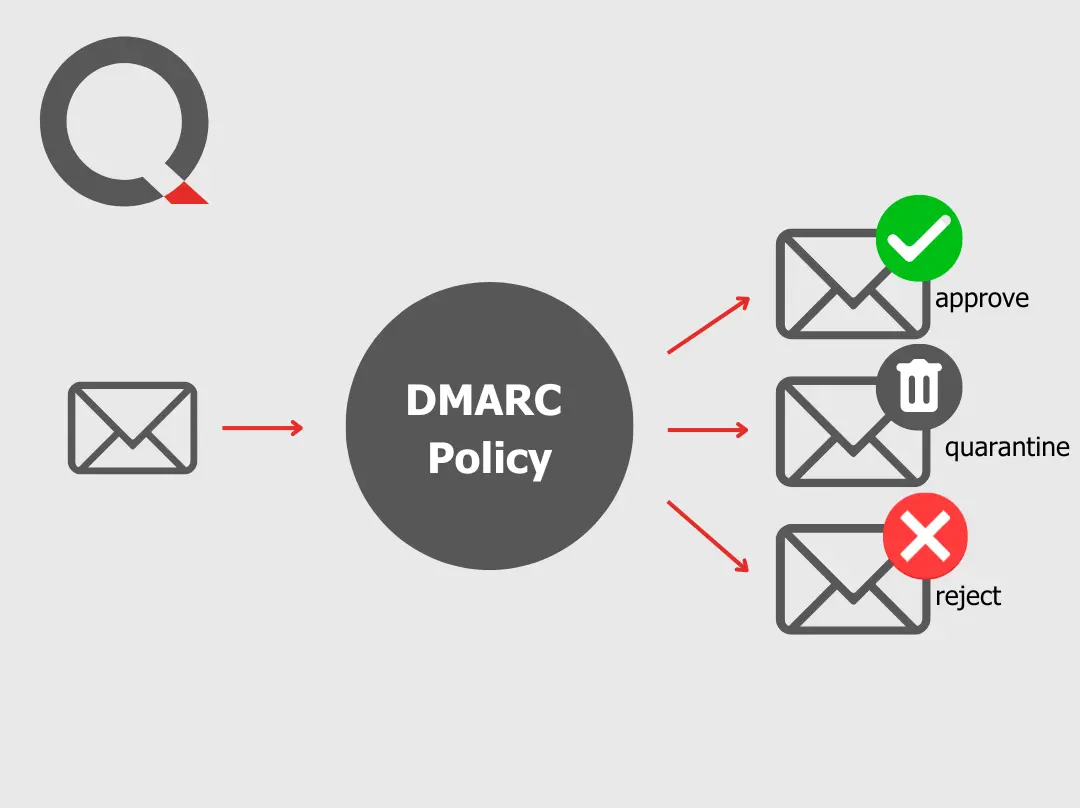
DMARC builds on top of DKIM and another email authentication protocol called SPF (Sender Policy Framework). It adds an additional layer of protection by enabling domain owners to specify policies for how their emails should be handled when they fail DKIM or SPF checks.
DMARC provides instructions to the receiving email server on how to treat emails that fail authentication checks, such as marking them as spam or rejecting them outright.
DMARC also includes reporting mechanisms that allow domain owners to receive feedback on email authentication results. These reports provide insights into who is sending emails on behalf of their domain and whether any unauthorized sources are attempting to send spoofed or fraudulent emails using their domain name.
By implementing DMARC alongside DKIM and SPF, organizations can enhance their email security, protect their brand reputation, and reduce the risk of phishing attacks and email fraud.
Why is it important for SAP Commerce?
E-mails such as order confirmations are usually sent by SAP Commerce with a sender address that uses the same domain as that of the employees of the company running SAP Commerce.
If the company wants to use DMARC and DKIM to protect against email spoofing it is required that also the Mails that are sent from SAP Commerce are signed with DKIM. If emails are not signed, mail providers like Gmail do not accept the emails or classify them as spam.
Example:
<someuser@gmail.com>: host gmail-smtp-in.l.google.com[XXX.XXX.XXX.XXX] said:
550-5.7.26 Unauthenticated email from storedomain.com is not accepted
550-5.7.26 due to domain's DMARC policy. Please contact the administrator of
550-5.7.26 storedomain.com domain if this was a legitimate mail.
550-5.7.26 Please visit
550-5.7.26 https://support.google.com/mail/answer/2451690 to learn about the
550 5.7.26 DMARC initiative.
How to implement this with SAP Commerce?
Based on Open Source Libraries we implemented a plugin for the OOTB Java and SAP Commerce Mail services.
If this plugin is installed all outgoing mails are automatically checked if a valid DKIM configuration exists for the domain of the sender address. If there is a valid configuration, the mail is automatically signed with the DKIM key.
If you are interested in this solution, do not hesitate to contact us.
Kontakt direkt
Querplex GmbH Nürnberg
Tel.: +49 (0)911 941198 0
Querplex GmbH Nürnberg
Kornmarkt 2
D-90402 Nürnberg